Secure healthcare website essentials for 2026
- Christian Hoover
- 3 days ago
- 9 min read

One in every two Americans had their medical records exposed in 2024 alone. That’s not a distant statistic, it’s your patients. 725 large healthcare breaches exposed 275 million patient records last year, with 80% traced directly to hacking and IT incidents. For med spas and wellness centers offering services like hormone replacement therapy, peptide treatments, and weight loss programs, the website is often the first and most vulnerable point of contact. If your digital infrastructure isn’t built for HIPAA compliance from the ground up, you’re not just risking fines, you’re risking your patients’ trust and your practice’s survival.
Table of Contents
Key Takeaways
Point | Details |
HIPAA security basics | A secure healthcare website must follow technical, administrative, and physical HIPAA safeguards. |
Technical must-haves | Encryption, MFA, audit logs, and BAAs with all vendors are now essential, not optional. |
Administrative diligence | Frequent risk analysis, staff training, and incident response planning are as vital as technology. |
Modern risks | APIs, tracking pixels, and insecure forms are common sources of PHI exposure and breaches. |
Continuous improvement | Ongoing reviews and adapting to regulation updates sustain true website security. |
What makes a healthcare website secure under HIPAA?
The word “secure” gets used loosely in web design circles. For healthcare, it has a precise legal meaning that goes well beyond an SSL certificate and a privacy policy page. HIPAA’s Security Rule divides required protections into three categories: physical safeguards, administrative safeguards, and technical safeguards. Your website touches all three.
A secure healthcare website must implement technical safeguards that include access control, audit controls, integrity measures, transmission security, and encryption, along with signed Business Associate Agreements (BAAs) for every vendor that handles Protected Health Information (PHI). PHI is any data that can identify a patient, including their name, date of birth, contact details, diagnosis, or treatment history.
For med spas and wellness centers specifically, PHI shows up in places that might surprise you:
Online intake and consent forms capturing patient health history
Appointment booking tools that store names, contact info, and service types
Before/after treatment photos linked to patient identifiers
Chat widgets or contact forms where patients describe symptoms or ask about treatments
Email marketing lists tied to specific treatment categories like TRT or HRT
“Most med spas don’t realize that their booking software, contact forms, and even their Google Analytics setup can all create HIPAA liability if PHI flows through them without a BAA in place.”
Consumer website builders like Wix and Squarespace are not built for this environment. They don’t offer BAAs by default, and their infrastructure wasn’t designed around HIPAA’s technical requirements. That’s not a criticism of those platforms; it’s simply the wrong tool for the job. The same logic applies to generic form tools, standard email marketing platforms, and off-the-shelf CRM systems. If you’re using any of these without a signed BAA, you’re operating outside HIPAA’s requirements.
Understanding SEO for healthcare businesses also connects here, your marketing infrastructure and your compliance infrastructure often share the same vendors and platforms. Getting both right at the same time is more efficient and far less risky.
PHI category | Common website touchpoint | Risk level |
Patient name + service type | Booking forms, CRM | High |
Before/after photos | Gallery, patient portal | High |
Health history responses | Intake forms | Critical |
Email + treatment category | Marketing lists | High |
IP address + page visited | Analytics (if PHI page) | Medium |
Core technical features of a secure healthcare website
Once you understand the regulatory framework, the next step is translating it into actual technology decisions. This is where most practices either get it right or leave massive gaps.
The baseline technical stack for a HIPAA-compliant healthcare website includes HTTPS with TLS 1.2+, HSTS, WAF, MFA for admin access, session timeouts, encryption at rest (AES-256), secure forms avoiding PHI in email, and audit logging. Each of these has a specific function, and skipping any one of them creates an exploitable gap.
Here’s what each element actually does for your practice:
HTTPS with TLS 1.2 or higher encrypts data moving between your patient’s browser and your server. Without it, form submissions travel in plain text.
HSTS (HTTP Strict Transport Security) forces browsers to always use the encrypted connection, preventing downgrade attacks.
WAF (Web Application Firewall) filters malicious traffic before it reaches your site, blocking SQL injection and cross-site scripting attempts.
Multi-factor authentication (MFA) for admin access means a stolen password alone can’t unlock your patient data.
Session timeouts automatically log out inactive users, protecting data on shared or unattended devices.
AES-256 encryption at rest protects stored data even if a server is physically compromised.
Secure forms route submissions directly to encrypted storage, never through standard email.
Audit logs create a timestamped record of who accessed what data and when.
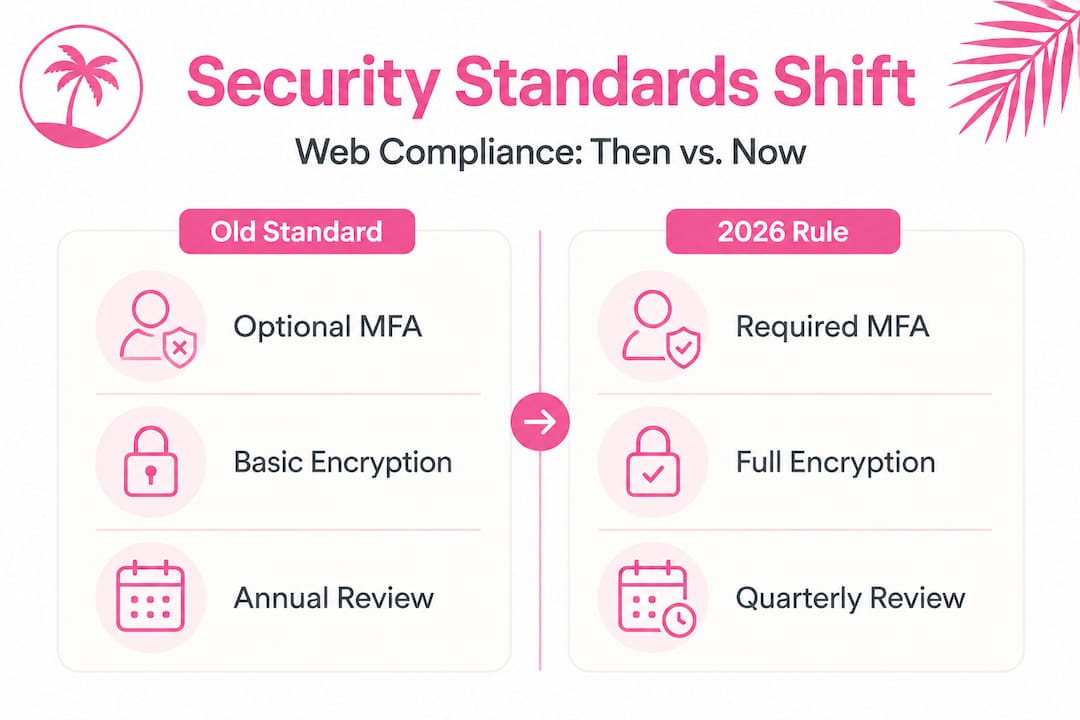
The regulatory environment is also tightening. The 2026 HIPAA NPRM proposes mandatory MFA, encryption at rest and in transit, immutable audit logs, quarterly log reviews, and monthly vulnerability scans. What were previously “addressable” items — meaning organizations could document a reason for not implementing them — are becoming hard requirements. If your secure healthcare site design was built two or three years ago, it may already be behind the curve.

Pro Tip: Run a free SSL check on your site using tools like SSL Labs. If you’re not scoring at least an “A” grade, your encryption setup needs attention before anything else. Then work your way up the checklist from there.
Feature | Old standard (addressable) | 2026 NPRM (required) |
MFA for admin access | Optional with justification | Mandatory |
Encryption at rest | Addressable | Required |
Audit log immutability | Recommended | Required |
Vulnerability scanning | Annual | Monthly |
Log review frequency | As needed | Quarterly |
Administrative safeguards: policies, risk analysis, and workforce training
Technology alone doesn’t create a secure environment. The administrative layer is where most small and mid-sized healthcare practices fall short, and it’s also where regulators look first during an audit.
Administrative safeguards under §164.308 require a documented risk analysis, workforce training, an incident response plan, and BAAs with hosting, forms, and analytics vendors. The risk analysis is not optional and it’s not a one-time exercise. It must be reviewed whenever you add a new vendor, change your website platform, or expand your service offerings.
Here’s a practical sequence for getting your administrative safeguards in order:
Conduct a formal risk analysis using the HHS Security Risk Assessment Tool (available free from HHS.gov). Document every system that touches PHI.
Audit all vendor relationships and confirm BAAs are in place for your hosting provider, booking system, CRM, email platform, and any analytics tools.
Train your team on PHI handling, specifically what not to send via email, how to handle patient photo requests, and what to do if they suspect a breach.
Create an incident response plan that specifies who gets notified, in what order, and within what timeframe if a breach occurs.
Schedule quarterly log reviews and monthly vulnerability scans as recurring calendar items, not ad hoc tasks.
Workforce training is consistently the weakest link. A front desk coordinator who emails a patient’s before/after photos through a standard Gmail account just created a reportable breach, regardless of how technically sound the rest of your infrastructure is. Training isn’t a one-time onboarding item — it needs to be reinforced regularly with real examples relevant to your specific services.
Pro Tip: When onboarding any new marketing or tech vendor, make it a standard part of your contract process to request and sign a BAA before any integration goes live. This applies to your web design for med spas partner, your SEO agency, and your CRM provider.
The connection between SEO compliance for providers and administrative safeguards is real. When your marketing team runs campaigns and uses analytics tools to track performance, those tools may be collecting data that crosses into PHI territory. That’s an administrative and technical risk that needs to be managed together.
Real-world risks: API breaches, tracking pixels, and PHI mishandling
The most dangerous vulnerabilities on healthcare websites right now aren’t dramatic cyberattacks. They’re quiet, technical missteps that go unnoticed for months. APIs, tracking pixels, and improperly configured forms are the primary culprits.
84.7% of healthcare organizations experienced an API security incident in the past year, with an average cost of $510,000 per incident. APIs (Application Programming Interfaces) are the connections between your website and third-party tools — your booking system, your patient portal, your CRM. When those connections aren’t properly secured, they become open doors.
Common vulnerabilities that lead to breaches include:
Misconfigured APIs that expose patient data to unauthorized third parties
Tracking pixels embedded by marketing platforms that capture PHI without a BAA
Standard contact forms that route submissions through unencrypted email
Weak or reused admin passwords without MFA protection
Outdated plugins or themes with known security vulnerabilities
The tracking pixel issue deserves special attention. Edge cases like tracking pixels — as seen in the Kaiser breach affecting 13 million patients — and non-BAA marketing tools highlight how easily PHI can be exposed. Kaiser used standard analytics pixels on pages where patients were logged in, and those pixels transmitted identifiable data to third-party ad platforms. The same risk exists for any med spa using standard Facebook Pixel or Google Tag Manager setups on pages where patients submit forms or access their records.
“If your marketing pixel fires on a page where a patient has entered their name, email, and the treatment they’re inquiring about, you may have just sent PHI to a third-party advertising platform without a BAA.”
Before/after photos are another underestimated risk. If a photo is stored in a folder linked to a patient name, appointment date, or treatment record, it qualifies as PHI. Storing those photos in a standard cloud drive or embedding them in a CMS without proper access controls is a compliance failure. Understanding compliance and advertising restrictions in the healthcare marketing context helps your team recognize where these risks intersect with your promotional activities.
Reviewing your marketing safeguards for providers is a practical starting point for identifying which tools in your current stack need BAAs or replacement.
Why secure healthcare websites require ongoing vigilance — not just ‘set and forget’
Here’s what most security guides won’t tell you directly: the “compliance mindset” is itself a security risk. When practices treat HIPAA compliance as a checklist to complete once and file away, they create a false sense of security that makes them more vulnerable, not less.
We’ve worked with med spas and wellness centers that had technically sound websites at launch — proper encryption, BAAs in place, secure forms — and still experienced breaches 18 months later because no one was monitoring the audit logs, a plugin update introduced a vulnerability, or a new marketing vendor was added without going through the standard BAA process. Security isn’t a destination. It’s a discipline.
The practices that maintain the strongest security posture aren’t necessarily the ones with the most sophisticated technology. They’re the ones that treat security as an ongoing operational responsibility. Monthly vulnerability scans, quarterly log reviews, annual risk analysis updates, and regular vendor audits — these aren’t bureaucratic exercises. They’re the activities that catch problems before they become breaches.
There’s also a cultural dimension that rarely gets discussed. When your front desk team, your injectors, your marketing coordinator, and your practice manager all understand why PHI protection matters — not just that it’s required — they make better decisions in the gray areas. They question whether it’s appropriate to text a patient about their HRT results. They flag a new software tool before it gets integrated. That kind of proactive culture is worth more than any single technical control.
The perspective on resilient site design we bring to every project starts with this principle: build for the long term, not just for launch day. A website that’s secure on day one but neglected on day 365 is a liability.
Want a secure and compliant website for your med spa or wellness center?
Translating all of these requirements into a functioning, patient-friendly website takes more than a checklist; it takes a team that understands both the regulatory environment and the specific operational realities of med spas and wellness centers.
At Citrus Ridge Marketing, we build med spa website design solutions that are HIPAA-aware from the ground up — secure forms, BAA-ready platforms, audit-ready configurations, and PHI-safe booking integrations. We also handle the marketing for med spas side, so your advertising tools and your compliance infrastructure work together rather than creating hidden risks. If you’re ready to build a digital presence that protects your patients and your practice, explore our wellness center digital marketing services and let’s map out a security roadmap specific to your center’s needs.
Frequently asked questions
What is considered PHI on a med spa or wellness website?
PHI includes intake forms, booking data, photos, and communications that can identify an individual patient — essentially any data that links a person to a health service or condition.
Can I use Wix or Squarespace for a HIPAA-compliant med spa website?
As of 2026, Wix does offer HIPAA compliant forms. Squarespace currently does not. CRM forms such as GoHighLevel for Healthcare do offer a BAA with their HIPAA add-on.
What is a BAA and why does my website vendor need one?
A BAA (Business Associate Agreement) is a legally binding contract that obligates your vendor to protect PHI under HIPAA. BAAs are required for all vendors that access, store, or transmit patient data on your behalf.
Is sending PHI via standard email or SMS allowed?
No. PHI must not be sent via standard email or SMS; only encrypted, HIPAA-compliant messaging systems meet the required standard for transmitting patient information.
How often should risk analysis and vulnerability scans be performed?
Under the 2026 HIPAA NPRM requirements, vulnerability scans should run monthly, audit logs should be reviewed quarterly, and a formal risk analysis should be updated at least annually or after any significant system change.
Recommended

Comments